React Markdown has become the go-to library for developers seeking a seamless way to display Markdown within React applications. It bridges the gap between raw Markdown syntax and the complex world of React components, offering a powerful solution for content-heavy applications. By parsing Markdown strings and converting them into valid HTML elements, it allows developers to maintain the simplicity of Markdown writing while leveraging the full power of the React ecosystem. This integration is particularly crucial for platforms like blogs, forums, or documentation sites where content flexibility meets interactive UI requirements.
The primary challenge often arises when developers need to mix HTML content directly with their Markdown. While standard Markdown is excellent for formatting text, sometimes it lacks the complexity required for advanced styling or specific structural elements. Questions frequently arise regarding whether this specific library can handle raw HTML tags embedded within the Markdown source. Understanding the capabilities and limitations of this parsing process is essential for building robust applications that require rich text rendering without compromising security or performance. The library handles this by providing options that can either allow or restrict HTML parsing based on specific configuration needs.
Furthermore, the security implications of rendering user-generated content cannot be overstated. Allowing arbitrary HTML execution opens the door to Cross-Site Scripting (XSS) attacks, making it a critical area of focus. React Markdown addresses these concerns through its default behavior and available plugins. By exploring how the library processes these mixed content types, developers can make informed decisions about how to configure their parsers. This ensures a balance between functionality, providing the ability to render complex layouts, and safety, protecting the end-user from malicious code injection.
Enabling HTML Content via Plugins
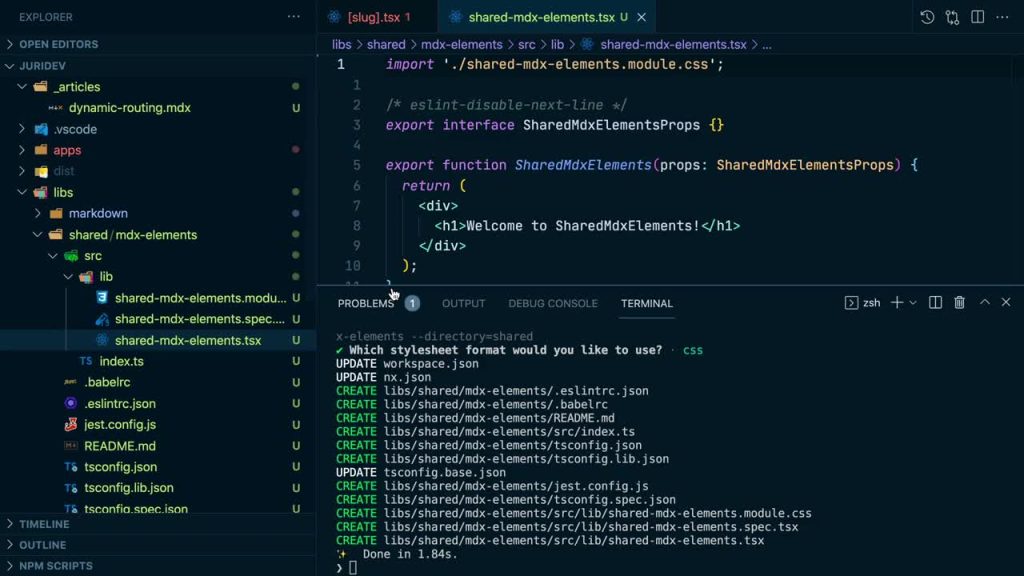
While the default configuration offers a basic toggle, the true power of extending React Markdown functionality lies in its plugin ecosystem. The library is designed to be extensible, allowing developers to add features through a system of plugins known as remark-plugins and rehype-plugins. These plugins hook into the parsing pipeline at different stages, enabling the transformation of the Markdown Abstract Syntax Tree (AST) before it is converted into React elements.
Using plugins allows for a more granular control over how content is processed compared to simple props. Plugins can intercept specific node types, modify their attributes, or even inject new nodes into the tree. This extensibility is essential for complex requirements that go beyond simple HTML rendering. It enables developers to implement custom sanitization rules, handle specific HTML tags differently, or integrate with other libraries that require processing the content before it reaches the DOM.
The use of plugins transforms React Markdown from a simple parser into a versatile content processing engine. By chaining multiple plugins together, developers can create a sophisticated rendering pipeline tailored to their specific needs. This modular approach keeps the core library lightweight while providing the necessary tools for advanced use cases. It separates concerns effectively, allowing the community to develop and share plugins that solve specific rendering challenges.
The Role of Rehype Raw
The rehype-raw plugin is the standard solution for enabling HTML rendering within React Markdown when using a more robust pipeline. While setting skipHtml to false works for basic cases, rehype-raw integrates deeply into the processing flow. It works by taking the HTML text nodes and parsing them into actual HTML nodes within the syntax tree. This allows subsequent plugins or the renderer itself to handle these HTML elements as native parts of the document structure.
To use this plugin, developers typically disable the default skipHtml behavior and include rehype-raw in the array of plugins passed to the components prop. This tells the parser that it should not skip over HTML strings but rather process them. The plugin ensures that the HTML is correctly nested and validated against the document structure. It provides a more reliable way to handle complex HTML than the native option, particularly when dealing with malformed or nested tags.
Furthermore, rehype-raw facilitates the use of other rehype plugins that might operate on HTML nodes. Once the HTML has been converted into nodes by rehype-raw, other plugins can sanitize, modify, or analyze these nodes. This creates a powerful pipeline where HTML content can be treated with the same level of scrutiny and manipulation as Markdown content. It is the preferred method for applications that require robust handling of mixed content types.
Sanitizing HTML with Rehype Sanitize
Security remains paramount when enabling HTML parsing, and rehype-sanitize is the counterpart to rehype-raw in this regard. This plugin acts as a filter, stripping out dangerous tags and attributes while allowing safe ones to pass through. It uses a schema to define which elements, attributes, and protocols are permissible. By including this plugin in the pipeline, developers can safely enable HTML rendering without exposing their application to XSS vulnerabilities.
The default schema provided by rehype-sanitize is conservative yet practical. It allows common tags like headings, paragraphs, and links while blocking scripts, iframes, and event handlers like onclick. Developers can customize this schema to be more permissive or restrictive based on their specific needs. For example, an application might allow class attributes for styling but strictly forbid style attributes to prevent CSS-based attacks or layout breaking.
Combining rehype-raw with rehype-sanitize provides a balanced solution. The raw plugin ensures the HTML is parsed and rendered, while the sanitize plugin ensures that only safe, approved HTML reaches the final output. This two-step process decouples the ability to render HTML from the security risks associated with it. It allows developers to give trusted users the power of HTML without compromising the safety of the broader platform.
Customizing Plugin Chains
The flexibility of React Markdown allows developers to chain multiple plugins to create a custom processing workflow. This means you can have a pipeline that includes rehype-raw for parsing, rehype-sanitize for cleaning, followed by other plugins for tasks like adding unique IDs to headings or syntax highlighting code blocks. The order of these plugins is critical, as each plugin transforms the output of the previous one in the chain.
- Plugins are passed as an array to the
remarkPluginsorrehypePluginsprops. - The order in the array determines the execution sequence during parsing.
- Custom plugins can be written to handle site-specific logic or transformations.
Customizing this chain allows for highly specific rendering behaviors. For instance, a developer might write a plugin that converts specific custom Markdown syntax into a React component, or one that automatically wraps external links in a target="_blank" attribute. By inserting these custom plugins into the chain, the rendering logic becomes highly tailored to the application’s requirements. This extensibility is what makes the library suitable for enterprise-level content management systems.
Ultimately, understanding how to construct and optimize these plugin chains is key to mastering React Markdown. It moves the developer beyond simple text rendering and into the realm of content engineering. By carefully selecting and ordering plugins, one can build a rendering engine that is secure, fast, and capable of handling the most complex mixed-content scenarios imaginable.
Custom Rendering with Components
One of the most powerful features of React Markdown is its ability to override the default HTML elements with custom React components. This is achieved through the components prop, which accepts an object mapping tag names to React components. Instead of rendering a standard <a> tag for a link, React Markdown can render a custom LinkButton component, allowing for deep integration with the application’s design system and routing logic.
This capability transforms the rendering process from a static display into a dynamic application feature. It allows developers to intercept specific elements and replace them with interactive components. For example, a standard Markdown image tag can be replaced by a sophisticated ImageGallery component that includes lazy loading, lightbox functionality, or zoom capabilities. This level of control ensures that the content fits perfectly within the broader user experience.
The custom components receive specific props, including the original HTML attributes and the children of the element. This provides the context needed to maintain the intended content while adding custom behavior. Whether it is styling every paragraph with a specific typography component or replacing code blocks with a syntax-highlighted editor, the components prop offers a direct bridge between Markdown syntax and the React component ecosystem.
Overriding Default Elements
The primary use case for the components prop is to override standard HTML elements. Developers might want to replace standard <p> tags with a custom Text component that handles typography scaling automatically. Similarly, <h1> through <h6> tags can be mapped to components that automatically generate table of contents entries or implement specific heading styles required by the design system. This ensures consistency across the entire application.
- Map tag names like ‘a’, ‘p’, ‘h1’ to custom React components.
- Pass specific props to these components to control behavior or style.
- Maintain accessibility by handling standard HTML attributes correctly.
When overriding elements, it is important to preserve the intended semantics of the original Markdown. While visual styles can change drastically, the underlying meaning of a header or a list should remain clear to screen readers and search engines. Custom components should pass through accessible attributes like aria-label or role to ensure that the rendered content remains inclusive. This attention to detail ensures that the custom implementation enhances the experience without breaking accessibility standards.
This mapping also allows for conditional logic. For instance, external links can be detected via their href attribute and rendered with an icon indicating they leave the site. Internal links can be handled by the application’s router, such as React Router, using a Link component instead of a standard <a> tag. This intelligent replacement makes the Markdown content feel like a native part of the Single Page Application (SPA).
Injecting Props and Context
Custom components used in React Markdown are not isolated; they can access the React context and receive additional props. This allows the rendered Markdown content to interact with the global state of the application. For example, a custom code block component might access a theme context to determine whether to render code in dark or light mode. This tight integration ensures that the content dynamically responds to changes in the application environment.
Developers can pass additional data to these components by wrapping React Markdown in a higher-order component or by using a custom context provider. This is particularly useful for features that require user authentication state or localization. A “Buy Now” button embedded within Markdown content could check the user’s login status via context and either render a checkout flow or a login prompt. This makes the content smart and interactive.
Furthermore, props passed directly to the React Markdown component can be forwarded down to the custom renderers. This allows for configuration on a per-instance basis. One instance of a Markdown renderer might allow image uploads, while another might be read-only. By passing these flags as props, the underlying custom components can adjust their behavior and UI accordingly, providing a highly flexible content rendering solution.
Handling Interactive Elements
Interactive elements within Markdown, such as checkboxes or specialized widgets, require careful handling. Standard Markdown does not support complex interactive UIs out of the box. However, by using the components prop, developers can detect specific syntax or HTML tags and render interactive components in their place. This blurs the line between content and application interface, allowing users to interact directly with the document content.
For example, a syntax like [ ] could be mapped to a custom Checkbox component that manages its own state and communicates changes back to the parent application. Similarly, a specific HTML tag could be replaced by a Chart component that visualizes data embedded in the Markdown. This capability turns static documents into dynamic dashboards where the content is not just read but acted upon.
It is crucial to manage the state of these interactive elements carefully. Since they are rendered dynamically, managing their state requires lifting the state up to the parent or using a state management library. This ensures that changes persist and can be saved back to the server. The ability to embed interactive elements directly within Markdown opens up new possibilities for educational tools, interactive documentation, and user interfaces.
Security Best Practices
Security is the most critical aspect of rendering user-generated content. The web is full of examples of sites that have been compromised by failing to sanitize input. When using React Markdown, or any library that parses text into HTML, security must be the top priority. This involves a defense-in-depth strategy where multiple layers of protection are implemented to ensure that malicious code never reaches the user’s browser.
The primary threat is XSS, where an attacker injects scripts that hijack user sessions or deface the website. Even if the source of the content is trusted initially, vulnerabilities in other parts of the system could allow an attacker to inject malicious content. Therefore, defense should never rely solely on the trustworthiness of the author. All content should be treated as potentially hostile until it has been rigorously validated and sanitized.
Best practices involve a combination of library configuration, plugin usage, and server-side validation. Relying solely on client-side sanitization is not enough, as client-side checks can often be bypassed. A comprehensive security strategy ensures that the application remains resilient against attacks, protecting both the users and the reputation of the platform. Understanding these threats is the first step toward mitigating them effectively.
Server-Side Sanitization
Before content even reaches the React frontend, it should be sanitized on the server. Server-side sanitization acts as the first line of defense. Libraries like DOMPurify or sanitize-html can be used on the backend to strip out dangerous tags and attributes before the data is stored in the database or sent to the client. This reduces the attack surface and ensures that malicious content is neutralized at the source.
Server-side validation is more secure because it operates in an environment that the user cannot directly manipulate. Unlike the browser, where a savvy user can modify JavaScript execution or bypass client-side checks, the server is under the full control of the application developer. Implementing strict sanitation rules here ensures that even if the frontend rendering logic changes or is misconfigured, the underlying data remains clean and safe.
This process should also handle cases where the content might be displayed in different contexts. By sanitizing at the storage level, you ensure safety regardless of where the content is eventually rendered—whether in a React app, a mobile API, or an email digest. This centralized approach to security simplifies maintenance and ensures consistent protection across all platforms and interfaces that consume the content.
Avoiding Dangerous Attributes
Even when using rehype-sanitize or similar tools, developers must be vigilant about specific attributes that can be vectors for attack. Attributes such as onclick, onload, onerror, and other event handlers can execute JavaScript code when specific events occur. CSS attributes like background-image using the url() function can also be used to inject scripts or track users inadvertently. Sanitization schemas must explicitly block these attributes.
- Event handlers like
onmouseovershould always be stripped from user input. - Javascript protocols in href attributes, such as
javascript:void(0), must be removed. - CSS properties that allow external resource loading should be restricted or carefully validated.
Furthermore, attributes like srcset or data-* can sometimes be abused if not handled correctly. Developers should rely on established, well-tested sanitization libraries rather than writing their own regex-based parsers. Writing a custom parser to strip HTML is notoriously difficult and prone to errors that attackers can exploit. Established libraries have been battle-tested against a wide array of edge cases and exploit attempts, providing a much higher level of security.
By maintaining a strict whitelist of allowed attributes, developers drastically reduce the potential for exploitation. The philosophy should be “deny by default, allow by exception.” Only attributes that are strictly necessary for the content formatting, such as href for links or alt for images, should be permitted. Everything else should be stripped out to prevent any possibility of script injection or unauthorized code execution.
Content Security Policy
Implementing a Content Security Policy (CSP) is a robust defense mechanism that works in conjunction with input sanitization. CSP is an HTTP header that tells the browser which sources of executable scripts are approved. Even if an attacker manages to inject a script tag into the rendered Markdown, the CSP will block the script from executing if its source is not in the whitelist. This provides a safety net for any sanitization failures.
A strict CSP might only allow scripts from the site’s own domain or a trusted CDN. It would block inline scripts entirely, which is a highly effective measure against XSS attacks. Configuring CSP requires careful planning, as overly restrictive policies can break legitimate functionality. However, for applications rendering user-generated Markdown, a strict policy is often worth the implementation effort for the security it provides.
CSP is not a replacement for input sanitization but a complementary layer. It creates a defense-in-depth strategy. If one layer fails, the next one steps in to prevent the damage. By combining server-side sanitization, client-side plugins like rehype-sanitize, and a strong Content Security Policy, developers can create a fortress around their application that protects users from a vast majority of web-based attacks.
Performance Optimization
Rendering complex Markdown documents that include HTML and custom components can be resource-intensive. Large documents with thousands of lines, or documents that process heavy plugin chains, can lead to interface lag. Performance optimization is crucial to ensure that the application remains responsive, even when dealing with substantial amounts of content. Users expect instant feedback, and slow rendering times can degrade the overall experience.
React Markdown is generally efficient, but the way it is used can impact performance significantly. The parsing process happens synchronously by default, meaning it blocks the main thread until complete. For small snippets of text, this is imperceptible. However, for large blog posts or technical documentation, this parsing time can become noticeable, leading to a janky user experience or freezing the interface momentarily.
Optimizing performance involves analyzing the rendering pipeline and identifying bottlenecks. This might involve optimizing the plugins used, modifying how components are rendered, or changing the parsing strategy. By addressing these areas, developers can ensure that their application remains snappy and capable of handling content-heavy pages without sacrificing the rich features provided by the Markdown parsing ecosystem.
Conclusion
React Markdown is a highly versatile tool that handles both standard Markdown and raw HTML content effectively. By leveraging its configuration options and the powerful plugin ecosystem, developers can fine-tune the parsing behavior to suit any specific requirement. The ability to render HTML adds a layer of flexibility for complex layouts, yet it necessitates a rigorous approach to security. Utilizing plugins like rehype-raw alongside rehype-sanitize ensures that functionality does not come at the cost of safety. Furthermore, implementing performance optimizations such as memoization and lazy loading guarantees that the user experience remains fluid and responsive. Ultimately, mastering these aspects allows developers to build secure, high-performance applications that deliver rich content seamlessly.